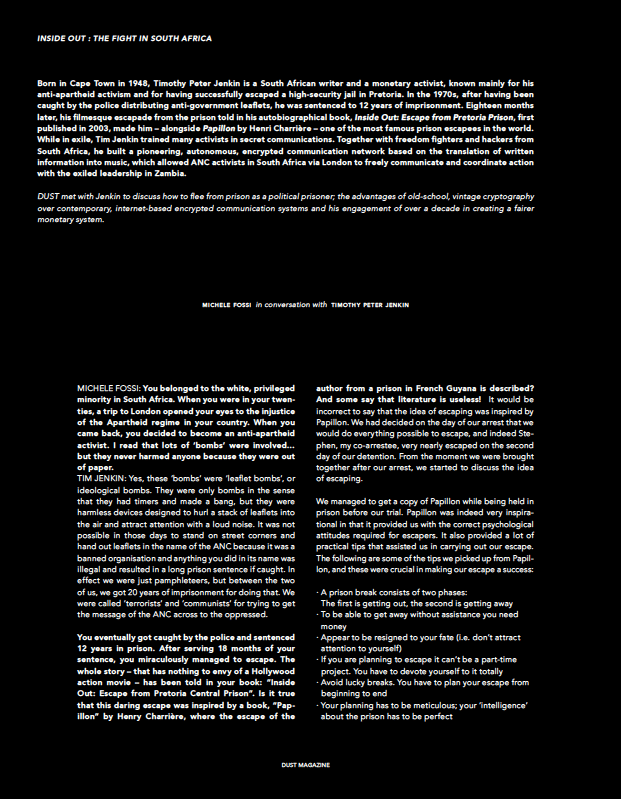
Born in Cape Town in 1948, Timothy Peter Jenkin is a South African writer and a monetary activist, known mainly for his anti-apartheid activism and for having successfully escaped a high-security jail in Pretoria. In the 1970s, after having been caught by the police distributing anti-government leaflets, he was sentenced to 12 years of imprisonment. Eighteen months later, his filmesque escapade from the prison told in his autobiographical book, Inside Out: Escape from Pretoria Prison, first published in 2003, made him — alongside Papillon by Henri Charrière — one of the most famous prison escapees in the world. While in exile, Tim Jenkin trained many activists in secret communications. Together with freedom fighters and hackers from South Africa, he built a pioneering, autonomous, encrypted communication network based on the translation of written information into music, which allowed ANC activists in South Africa via London to freely communicate and coordinate action with the exiled leadership in Zambia.
DUST met with Jenkin to discuss about how to flee from prison as a political prisoner; the advantages of old-school, vintage cryptography over contemporary, internet-based encrypted communication systems and his engagement of over a decade in creating a fairer monetary system.
Michele Fossi: You belonged to the white, privileged minority in South Africa. When you were in your twenties, a trip to London opened your eyes to the injustice of the Apartheid regime in your country. When you came back, you decided to become an anti-apartheid activist. I read that lots of ‘bombs’ were involved… but they never harmed anyone because they were out of paper.
Peter Jenkin: Yes, these ‘bombs’ were ‘leaflet bombs’, or ideological bombs. They were only bombs in the sense that they had timers and made a bang, but they were harmless devices designed to hurl a stack of leaflets into the air and attract attention with a loud noise. It was not possible in those days to stand on street corners and hand out leaflets in the name of the ANC because it was a banned organisation and anything you did in its name was illegal and resulted in a long prison sentence if caught. In effect we were just pamphleteers, but between the two of us, we got 20 years of imprisonment for doing that. We were called ‘terrorists’ and ‘communists’ for trying to get the message of the ANC across to the oppressed.
2. You eventually got caught by the police and sentenced 12 years in prison. After serving 18 months of your sentence, you miraculously managed to escape. The whole story – that has nothing to envy of a Hollywood action movie — has been told in your book : “Inside Out: Escape from Pretoria Central Prison”. Is it true that this daring escape was inspired by a book, “Papillon” by Henry Charrière, where the escape of the author from a prison in French Guyana is described? And some say that literature is useless!
It would be incorrect to say that the idea of escaping was inspired by Papillon. We had decided on the day of our arrest that we would do everything possible to escape, and indeed Stephen, my co-arrestee, very nearly escaped on the second day of our detention. From the moment we were brought together after our arrest, we started to discuss the idea of escaping.
We managed to get a copy of Papillon while being held in prison before our trial. Papillon was indeed very inspirational in that it provided us with the correct psychological attitudes required for escapers. It also provided a lot of practical tips that assisted us in carrying out our escape. The following are some of the tips we picked up from Papillon, and these were crucial in making our escape a success:
● A prison break consists of two phases: (1) getting out; (2) getting away
● To be able to get away without assistance you need money
● Appear to be resigned to your fate (i.e. don’t attract attention to yourself)
● If you are planning to escape it can’t be a part-time project. You have to devote yourself to it totally
● Avoid lucky breaks. You have to plan your escape from beginning to end
● Your planning has to be meticulous; your ‘intelligence’ about the prison has to be perfect
● When you are out, get as far away as quickly as possible
● When you are out, do not go anywhere your captors might expect you to go
● You need ‘civilian’ clothing. You can’t look like an escaped convict!
● Do not use violence against the prison guards; avoid them completely if possible
● Try to leave no clues about how you escaped
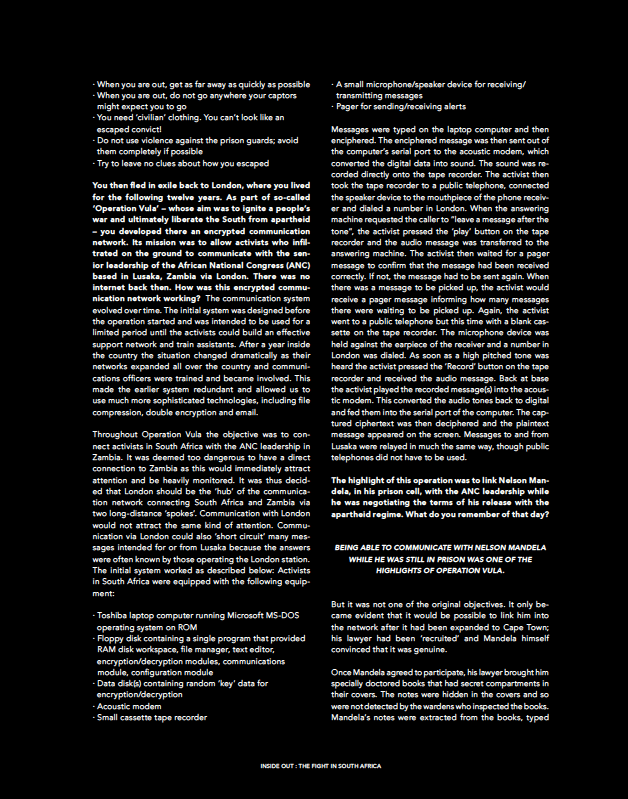
3. You then fled in exile back to London, where you lived for the following twelve years. As part of so-called ‘Operation Vula’ — whose aim was to ignite a people’s war and ultimately liberate the South from apartheid — you developed there an encrypted communication network. Its mission was to allow activists who infiltrated on the ground to communicate with the senior leadership of the African National Congress (ANC) based in Lusaka, Zambia via London. There was no internet back then. How was this encrypted communication network working?
The communication system evolved over time. The initial system was designed before the operation started and was intended to be used for a limited period until the activists could build an effective support network and train assistants. After a year inside the country the situation changed dramatically as their networks expanded all over the country and communications officers were trained and became involved. This made the earlier system redundant and allowed us to use much more sophisticated technologies, including file compression, double encryption and email.
Throughout Operation Vula the objective was to connect activists in South Africa with the ANC leadership in Zambia. It was deemed too dangerous to have a direct connection to Zambia as this would immediately attract attention and be heavily monitored. It was thus decided that London should be the ‘hub’ of the communication network connecting South Africa and Zambia via two long-distance ‘spokes’. Communication with London would not attract the same kind of attention. Communication via London could also ‘short circuit’ many messages intended for or from Lusaka because the answers were often known by those operating the London station.
The initial system worked as described below:
Activists in South Africa were equipped with the following equipment:
● Toshiba laptop computer running Microsoft MS-DOS operating system on ROM
● Floppy disk containing a single program that provided RAM disk workspace, file manager, text editor, encryption/decryption modules, communications module, configuration module
● Data disk(s) containing random ‘key’ data for encryption/decryption
● Acoustic modem
● Small cassette tape recorder
● A small microphone/speaker device for receiving/transmitting messages
● Pager for sending/receiving alerts
Messages were typed on the laptop computer and then enciphered. The enciphered message was then sent out of the computer’s serial port to the acoustic modem, which converted the digital data into sound. The sound was recorded directly onto the tape recorder. The activist then took the tape recorder to a public telephone, connected the speaker device to the mouthpiece of the phone receiver and dialed a number in London. When the answering machine requested the caller to “leave a message after the tone”, the activist pressed the ‘play’ button on the tape recorder and the audio message was transferred to the answering machine. The activist then waited for a pager message to confirm that the message had been received correctly. If not, the message had to be sent again. When there was a message to be picked up, the activist would receive a pager message informing how many messages there were waiting to be picked up. Again, the activist went to a public telephone but this time with a blank cassette on the tape recorder. The microphone device was held against the earpiece of the receiver and a number in London was dialed. As soon as a high pitched tone was heard the activist pressed the ‘Record’ button on the tape recorder and received the audio message. Back at base the activist played the recorded message(s) into the acoustic modem. This converted the audio tones back to digital and fed them into the serial port of the computer. The captured ciphertext was then deciphered and the plaintext message appeared on the screen. Messages to and from Lusaka were relayed in much the same way, though public telephones did not have to be used.
4. The highlight of this operation was to link Nelson Mandela, in his prison cell, with the ANC leadership while he was negotiating the terms of his release with the apartheid regime. What do you remember of that day?
Being able to communicate with Nelson Mandela while he was still in prison was one of the highlights of Operation Vula, but it was not one of the original objectives. It only became evident that it would be possible to link him into the network after it had been expanded to Cape Town; his lawyer had been ‘recruited’ and Mandela himself convinced that it was genuine.
Once Mandela agreed to participate, his lawyer brought him specially doctored books that had secret compartments in their covers. The notes were hidden in the covers and so were not detected by the wardens who inspected the books.
Mandela’s notes were extracted from the books, typed up and then encrypted and sent through our communication channels. I had no warning that his reports were going to be coming through London so it came as an incredible surprise one day when a long report from Mandela suddenly deciphered into clear text on my computer screen. I felt so honoured to be the first person outside South Africa to be able to read his reports.
There were many reports sent this way, going to and coming from the ANC leadership in Lusaka.
Mandela was discussing the terms of his release as well as the general political situation with leading figures of the apartheid regime. The regime thought that they had Mandela nicely isolated in the prison and that the views he espoused were his own. Little did they know that everything he said was in fact the ‘party line’. In this way Vula assisted in preventing the split that the apartheid regime was trying to create between Mandela and the ANC leadership in exile.
5. Nearly 30 years later, which instruments of encrypted communications do resistance groups in the world mainly use today? What are the major differences with respect to Operation Vula?
I’m afraid I can’t answer these two questions because I don’t know. In the 1980s, before the internet era, there were almost zero secure communication options so you had to invent your own. That is what we did with Vula and why the story of Vula stands out so clearly in the history of liberation struggles.
Today there are so many different communication options it is just a matter of choosing the best one for your needs. A lot of secret communication today involves the use of messaging apps, such as Telegram, Signal, Wire etc. There are many freely obtainable encryption tools, so what took great effort 30 years ago is now easy.
However, nothing today has the anonymity of the Vula communication system, which had nearly no metadata attached that could give the game away. Vula was ‘hand-crafted’ and designed to do a specific job for a specific set of circumstances. We knew it was secure because it was our own and we did not rely on software that could have been compromised or was malware.
Today’s technologies make Vula look primitive, but Vula was unique because it operated almost completely ‘off grid’ and outside of conventional channels. It was not reliant on software developed by companies that might have been working hand in hand with our enemies.
In the first years of the twenty-first century, you saw a new form of oppression in your country and in the world: the monetary system. Your answer was “Community Exchange Systems”, a free, open-source software that now has 50,000 users, in over 700 locations worldwide. Instead of units of ‘money’ being issued into circulation according to a policy or algorithm, peers extend credit to each other. It means people who have little money but have time, skills and resources can start helping each other and trading with each other without official money. Dr Jem Bendell, Professor of Sustainability Leadership and Founder of the Institute for Leadership and Sustainability (IFLAS) at the University of Cumbria (UK), has called it a ‘collaborative credit’, as it involves members of a network trusting each other rather than a bank. Can you give us a deeper insight into this new battle of yours?
After the fall of apartheid we expected to see a new South Africa that was very different from the old, but after five or so years it became clear that not much had really changed. The worst aspects of apartheid had disappeared and in theory everyone was equal, but in reality not very much had changed!
It soon dawned on many that winning the political struggle was the lesser part of the overall struggle against ‘the system’. Overall control remained in the hands of those who wielded economic power, and those at the top of the pyramid were the mining, corporate and financial institutions that defined the direction of development and controlled government.
The ‘money power’ remained in control and the government functioned to keep the structure in place. As this control mechanism was linked to global financial institutions, replacing the apartheid government with a ‘democratic’ one changed very little.
So the question was how to create a new society that is not controlled by the ‘money power’ and their government enforcers. Overthrowing governments achieves nothing if the real power is not in the hands of governments. It is the wrong target!
Many people came to the realisation that those who control the means of exchange (those who exert control over the money system) control everything. There is no way of ‘overthrowing’ and taking control of the money system (exchange system), so why not create an alternative exchange system that is truly democratic, without ‘owners’ and ‘controllers’ apart from those who use it.
In 2003 the Community Exchange System (CES) was launched. Its aim was to create a way to exchange what people have and can do without using conventional money. This is not a ‘barter system’ simply because money is not used. It is a true exchange system that does what money does, but without any controllers and manipulators who use the means of exchange for their own advantage.
Money itself is a relic from the past, where physical objects (gold, silver, bullion) were said to represent value. In the modern era we still carry around in our heads the idea that there is this ‘stuff’ called ‘money’ that is as essential to life as air and water. But it is just an idea. Today money does not exist. It is just numbers on computers and in our heads.
Banks wish to keep alive the notion that money exists so that they can continue lending it to us at interest. But why keep up the pretence that money exists when it is just an accounting system recording the transfer of value from one party to another?
The Community Exchange System is exactly what its name implies. It is community based and permits members of a community to trade with each other without using bank/government money. While being community focused it still permits global trade, but without interest and intermediate ‘fees’ and ‘tolls’.
It is a truly democratic exchange system with no one in control and benefiting off the trades of others. It is the basis of a truly democratic society without enforcers, controllers and parasites!
8. According to an article by Thomas L. Friedman that appeared on the New York Times last January, quantum computers – a new, significantly more powerful generation of computers exploiting principles borrowed from quantum physics – will reach the markets much sooner than initially announced – some say even in just ten years from now. Such computers could crack easily even the most reliable encryption systems in use today. Are hackers already preparing themselves for the ‘post-quantum era’? Are there any projects you are particularly fond of?
I am not really following developments in the world of cryptography so I can’t comment on what impact quantum computing will have on current encryption systems. All I know is that when someone comes up with a way to undermine prevailing encryption systems, someone else will come up with another way to ensure privacy.
In Operation Vula we used one of the simplest encryption algorithms known, but one that is theoretically unbreakable. This is the ‘one-time pad’ system. Even the most powerful quantum computers will never be able to defeat this system because every possible answer is correct, and no one can know which is the correct one!
With the one-time system, the key is as long as the message. This means that each character of a file is encrypted on its own, and has no connection with the next character. An encrypted character can thus decrypt to any other character and there is no mathematical way of determining what the correct character is. This renders the system unbreakable.
The one-time system of course comes with a terrible key distribution problem and strict rules about never using the same keys more than once. Nonetheless, cryptographers might have to ‘reinvent’ the one-time system to ensure that quantum or any future supercomputers are powerless to do anything.
9. In May 2017 it was announced that we’ll finally be able to see your story as a movie based on your book. The production, with Harry Potter star Daniel Radcliffe playing your role and David Barron as a producer, is expected to start this year. Which aspect of the story in particular do you hope will be told faithfully? Which impact do you hope this movie will have on people who today have the age that you had when you were exploding your ‘leaflet bombs’?
I am not expecting the film to be a faithful record of our escape. It is going to be a fictionalised version of our escape experience. It is difficult to tell in 100 minutes a story as long and complicated as the one described in my book, so parts of the story will be conflated by using imaginary occurrences.
However, I hope that the film will get across how complicated the escape was, how detailed it was, how unique it was, how fearful it was, and that our motivations were political and not just a flight from the unpleasantness of incarceration.
I hope that the film will carry various messages: that life is a series of barriers (doors) that we have to overcome before we reach our goal (front door); that with persistence, determination and meticulous attention to detail, any goal can be achieved; that goals can’t be achieved just by thinking about them; that practice informs the theory about how we achieve our goals.
Published on DUST 13 – We have no fathers